
Cyber crime is now the fourth most reported economic crime in SA, according to the findings of PwC's 2016 Global Economic Crime Survey.
Almost a third (32%) of the 232 South African organisations that took part in the survey reported cyber crimes in the last 24 months. This puts local companies on par with their international counterparts when it comes to cyber crime.
The country leads the global stats for economic crimes, with 69% of local companies having experienced economic crime during the past two years, compared with the global average of 36%.
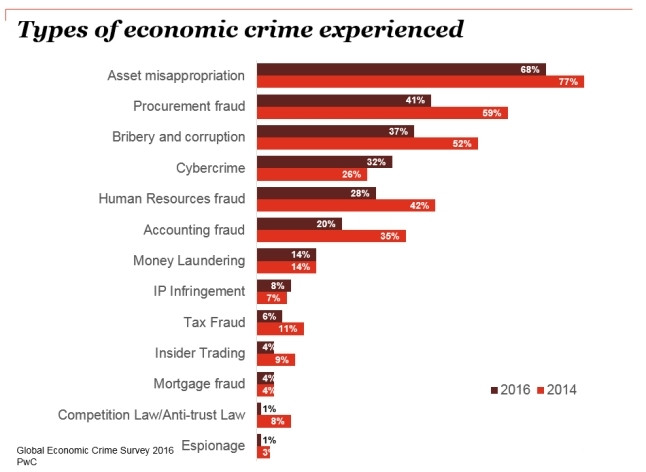
Speaking at the media launch of the survey, PwC director Trevor White said: "SA's incidence of economic crimes has remained stable, but the reporting of most categories of economic crime went down in the last two years, with the exception of cyber crime. It was the only area that showed an increase (from 26% of respondents in 2014 to 32% in 2016). Globally, cyber crime is the second-most reported economic crime."
On the rise globally
France (68%), Zambia and Kenya (both 61%), the United Kingdom and Spain (both 55%), Australia (52%), the Russian Federation (48%), and the Netherlands and Belgium (both 45%) make up the rest of the top 10 nations that are victims to economic crimes.
White said: "Cyber crime on its own has changed France's statistics to the top five, from not even being in the top 10 in the previous survey."
He cautioned against blaming government for all economic crimes, saying: "Economic crime is as much a private sector as a public sector problem - only 17% of respondents were from government and state-owned enterprises. That means 83% of respondents were in the private sector and should also take responsibility for reducing economic crimes."
The survey found asset misappropriation was the most prevalent economic crime, reported by 68% of respondents. Procurement fraud (41%) and bribery and corruption (37%) make up the balance of the top three reported economic crimes in SA.
The survey interviewed 6 337 participants in 115 countries. Globally, the overall rate of economic crime reported has fallen for the first year since the financial crisis, but only marginally from 37% in 2014 to 36% in 2016.
Big money at stake
White said the monetary amounts lost were also concerning. Around 25% of South African companies that suffered an economic crime in the last 24 months had lost more than $1 million, while the global average was 13%. "Organisations that lost more than $100 million in SA was 2% but globally only 1% of organisations lost more than $100 million. The effect on the economy is enormous, and these figures don't take into account collateral damage like loss of staff morale."
There was a significant shift in SA to external perpetrators, which now make up 46% (from 38% in 2014) of attacks, with internal actors making up 45% of perpetrators (61% in 2014), noted White.
Louis Strydom, forensic services leader for PwC Africa, said: "Cyber criminals are virtually always external, which could be contributing to this change."
Of concern was local organisations' approach to economic crime in general and cyber crime specifically: "What do businesses do when they detect an economic crime? 66% use their own people to investigate, and taint the evidence in the process. As a result, convictions are low," White said.
PwC Africa's Junaid Amra said cyber crime was no longer geographically specific, had permeated across all industries, and that "board awareness seems to be lacking". He called for companies to include cyber crime awareness in their business continuity plans.
No response plans
"In SA, 32% of companies have been victims of cyber crime and 57% think they will be affected in the next two years. But only 35% of organisations have incident response plans for the risk they perceive," Amra said.
He said 61% of global CEOs were concerned about cyber security but less than half of board members requested information about their organisation's state of cyber-readiness.
PwC separates cyber crimes into two broad categories: cyber fraud (monetisable cyber crimes such as credit card and identity theft) and transfer-of-wealth/IP attacks, designed to target the intellectual property (such as trade secrets, product information, negotiating strategies) of organisations. Despite their high profile, cyber fraud cases rarely pose an existential threat to companies, while transfer-of-wealth/IP attacks are not only difficult to detect but their damage could extend to billions of dollars, including wiping out whole lines of business, a company or even a larger economic ecosystem.
There were five main threat actors: nation-states (espionage, victims are other governments or agencies), insiders (employees and trusted third parties with access to sensitive data), terrorists (relatively nascent threat, usually victims are governments or infrastructure such as electricity grid or water systems), organised crime syndicates (victims are financial institutions, retailers, medical and hospitality companies) and hacktivists (victims include any organisation that invoke the hacktivists' ire).
Amra said around 33% of attacks came from employees, and 33% from trusted third parties. "Hacktivism has been ramping up since 2009. In the last two weeks, anonymous.com launched attacks on African governments, and a while ago, the sponsors of the World Cup in Brazil were attacked by Hactivist and Anonymous. Given all the threats, it's surprising that 12% of organisations don't intend to implement a response plan, and 13% didn't know if they were going to implement a response plan."
Attacker alert
He said on average, attackers spend 180 to 200 days on victims' networks, mainly because "the first responders to cyber crimes are heavily weighted to the IT side, and getting the network back up, rather than forensic solutions. Attackers launch multiple attacks, some diversionary, and while the IT team works to keep the system running, the real attack happens, stealing the intellectual property of the organisation."
Amra expressed concern that a common trait across companies that had breaches was that "the level of board buy-in was poor ? only 5% of board members receive info on cyber security monthly".
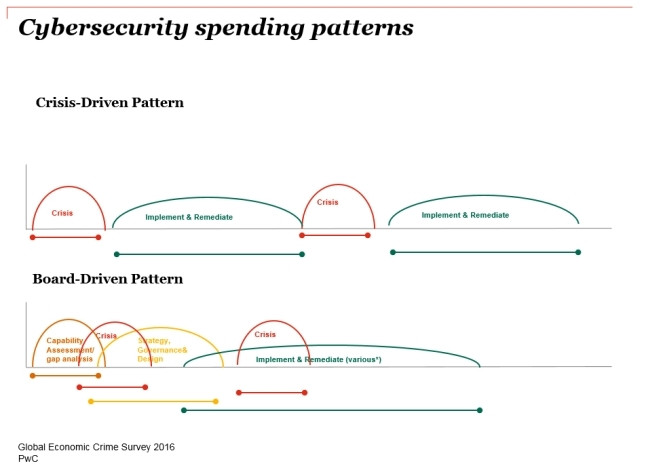
"We see two types of organisation emerging: those with and those without board involvement in cyber crime initiatives. Where the response to cyber crime is board-driven, there is a system of governance in place, and neither the response nor the security spend is crisis-driven."
To help boards better visualise the implications of cyber crimes, PwC has developed The Game of Threats, an electronic simulation of a cyber attack where half of board members are attackers and half are responding to the attack.
"Cyber security is not an IT issue - involvement from the executive level is critical because current incident response plans are not surviving contact with the real world," Amra said.
Share