Johannesburg, 20 Nov 2017
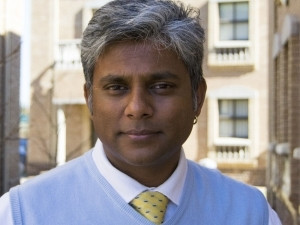
Devices - or things - are the most talked-about subject at the majority of IT conferences around the globe today, says Shailendra Harri, Business Development at CHM Vuwani. "From biochip tracking devices for animals, to wearable devices, fridges, motor vehicles, workstations, servers, automated blinds, garden sprinkler systems, heart monitoring implants... the list keeps growing."
Simply put, the Internet of things (IOT) allows objects to be sensed or controlled remotely via the Internet. Sensors collect useful and, in some cases, critical and even sensitive data with the help of various existing technologies that they are connected to. This data can then be shared between other devices.
As extensive as the myriad possible IOT applications are across all industries, the security of IOT has to be of concern, continues Harri. He alludes to the American television series 'Mr Robot' as a prime example of what can go wrong. "Mr Robot, the lead character, hires a team to hack into the environmental controls of a global business's data centre, with a view to causing it to overheat, thereby frying all of its electrical components and destroying all of the business's data, and ultimately, cancelling all consumer debt."
The series is based on the premise of using hacking to bring about social change, and serves to illustrate just how IOT has opened up new avenues for cyber attacks, regardless of the motive behind them.
Three things to consider about IOT security
1. Experts estimate the IOT market will consist of about 30 billion objects by 2020 and 50 billion by 2022.
While the key driver behind IOT is data, the thinking behind IOT is improved efficiency, accuracy and economic benefit with reduced human intervention. "When IOT is augmented with sensors and actuators, it possesses truly innovative capabilities. However, the technology becomes riddled with security vulnerabilities that hackers can easily exploit," says Harri. "As more devices with weak or no security connect to the Internet, the world will become more vulnerable to attacks."
2. In recent years, there's been a massive growth in the global cyber threat and there's been a significant rise in the exploitation of IOT technologies.
In 2014, thousands of home security cameras were hacked and live-streamed online. This type of hack was also used for spying on government officials. The subverting of security systems is a popular topic at conferences, with some legacy systems still in use and vulnerable to attack.
A motor vehicle company's smart vehicle system was hacked in 2015 and resulted in a mass recall, with some vehicles being hacked while they were being driven. "This goes beyond the ability to remotely unlock your vehicle, and extends as far as being able to control the engine from a distance, a frightening and dangerous prospect," says Harri.
IOT applications that are meant to improve efficiency and that are transforming businesses around the world are instead increasing the likelihood of a cyber attack on those organisations. Things like mobile, social media, cloud, analytics and connected devices are changing people's lives and the way in which things are done, but they are equally making them vulnerable to attack. When you add the increased data speeds that are now available, the threat is able to spread faster than ever.
3. IOT is a giant network of connected 'things' that also includes people. The relationships will be between people-people, people-things and things-things.
Harri says: "The decisions you make today will determine your business's security standpoint going forward, as well as how much faith your stakeholders have in your organisation's ability to protect them, their data and their devices."
How exactly does IOT impact you?
If a hacker can access your entire network via your connected toaster, fridge or security camera, then you need to take action. Harri says: "Security - particularly cyber security - is a major concern, but is usually the last topic to be brought up. With billions of devices being connected together, can you confidently say that your data is secure?"
IOT network security solutions
Solutions can protect your IOT networks work by collecting, sorting, monitoring and normalising data from IOT devices, generating actionable data that can be used to proactively reduce the risk of cyber storms. There are several IOT security measures that you can deploy to protect your brand reputation. These include:
* Threat detection - detect, block and respond to threats
* Device hardening - the device has its own security layer
* Identity access management - control who can access what
* Authentication on both hard and soft tokens - two-factor authentication
* Encryption - of the data on devices and in transit
* Security analytics - collecting data to enable predictive reporting and alerting
* Visibility solutions - know at all times what is happening with your devices
* Data protection solutions - keeping sensitive data safe
* Application scanning - constant monitoring to ensure applications are not compromised
"IOT brings with it the challenge of potentially managing hundreds, thousands and even - in bigger organisations - millions of devices," says Harri. "It's essential to create complex policies and ensure that your IOT security partner has the ability to scale with your business."
Share
