South Africa is the most targeted country in Africa when it comes to distributed denial-of-service (DDOS) attacks.
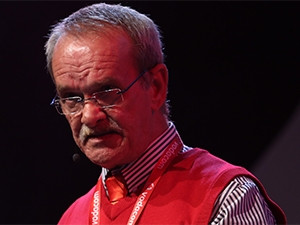
This was revealed by Vernon Fryer, chief technology security officer at Vodacom, in a keynote address during ITWeb Security Summit 2015, in Midrand, this morning.
In computing, a DDOS attack is an attempt to make a machine or network resource unavailable to its intended users. Such an attack generally consists of efforts to temporarily or indefinitely interrupt or suspend services of a host connected to the Internet.
Fryer was speaking with reference to statistics from the Vodacom Cyber Intelligence Centre, which the company established eight years ago to analyse the threat landscape on the African continent. He revealed over the past 18 months, there has been a marked increase in DDOS attacks on the continent, with a typical attack averaging 9Gbps.
"There has been about a 150% increase in the number of DDOS [attacks] in the last 18 months in Africa," he said.
In terms of the number of attacks, Kenya, Uganda, Algeria, Nigeria and Tanzania respectively come after SA, said Fryer, pointing to the analysis done by the Vodacom Cyber Intelligence Centre last Thursday.
According to Fryer, the majority of in-bound traffic to SA emanated mainly from China, Germany, Brazil, Vietnam, Russia, Cyprus, Turkey, Switzerland, Canada and the US. However, he noted, it was surprising Switzerland and Canada were featuring on the list this year, something never witnessed previously.
Another unexpected trend showed traffic coming from Swaziland, he added.
Describing some of the attack vectors cyber criminals were making use of in the region, Fryer pointed to scareware, ransomware, fake anti-virus, as well as TDSS Rootkit, among others. The trending malware included KINS Trojan, Skypot, VirRansom, SpyEye Trojan and the Chameleon Botnet.
With regard to ransomware attacks in Africa, Tanzania is the most attacked on the African continent, Fryer said.
He also noted the trending hacker groups in Africa include Anonymous, also known as the Lizard Squad, the Syrian Electronic Army, as well as the Yemen Cyber Army.
Faced with the rise in the level and sophistication of attacks, Fryer said organisations need to constantly monitor the behaviour of their firewalls.
Typically, he said, organisations take about five years without monitoring their firewall. "We need to understand if our firewalls are capable of handling today's threats. Thus, the performance of firewalls needs to be constantly monitored," he concluded.
Share