A new security flaw in the South African National Roads Agency's (Sanral's) e-toll Web site exposes registered users' personal details, leaving them vulnerable to criminal activity.
Exploiting the flaw, attackers could - until this morning - gain access to unsuspecting victims' accounts, including their personal data such as car registration, phone numbers, physical address and other information.
The exposed data is ripe for exploitation - it could be used to initiate fraud, phishing, identity theft, or even housebreaking, particularly when coupled with records of a user's driving habits.
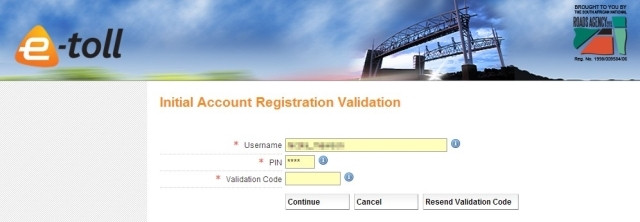
The flaw was exposed at the end of 2013 by a researcher identifying himself as "Moses Thembeka" and "moe1". The researcher published an advisory and a video showing how to capture the PIN of a registered e-toll user.
The flaw does not require any special tools or software to exploit, nor does the attacker need a registered e-toll account. Sanral hastily patched the flaw after widespread social media exposure and media questions about the vulnerability, but many user accounts may have already been compromised.
While the agency has yet to provide detailed commentary on the privacy breach, it yesterday claimed to have signed up almost a million e-tag users, all of whose details will be registered on the site. ITWeb demonstrated the latest security issue in a previous attack, showing that a motorist, tagged or not, could be tracked in real time by exploiting a flaw in the e-toll Web site.
Risky business
Since the latest hack requires an attacker to know or guess a victim's username, the number of accounts likely to be compromised could be relatively low, but the risk to hacked accounts is very high.
Sanral responds:
Sanral spokesperson Vusi Mona responded to the Web site flaw post publication: "Sanral strongly condemns the cyber attack on the online e-toll account management Web site. Our technicians worked flat out yesterday to resolve this security issue and an intervention has been successfully deployed to ensure that login details for online account management is secure.
Mona says Sanral will investigate the legal options it can take in the wake of what he refers to as attacks.
"Some people may not like e-tolls but launching an attack on law-abiding citizens, just because they registered an e-toll account, is appalling.
"Sanral would like to assure road users that it will continue to look at innovative measures to ensure the protection of road user data."
E-toll customers using common names or words as usernames would be most at risk. ITWeb tested this theory and successfully accessed a number of accounts in a matter of minutes (and notified the users in question).
And, since registrations on the e-toll Web site are restricted to a limited, non-case-sensitive character set for usernames, it would be plausible for a potential attacker to brute force a large amount of the namespace with little effort - the Sanral database is a goldmine for criminal syndicates, especially if there are nearly a million e-tags in circulation, as Sanral claims.
The phenomenon of password reuse is also a probable issue, with users likely to reuse familiar PINs for bank cards, cellphones, home alarms and so on.
Privacy problem
Although the flaw has been patched, this will be scant consolation to anyone whose personal details have been stolen. Sanral could easily identify potential victims by analysing its site logs to find accounts subjected to the PIN identification process, and accounts that have been accessed from multiple IP addresses, in order to notify them of a possible breach.
However, until the mandatory disclosure requirements of the Protection of Personal Information (POPI) Act come into effect, the agency is not obligated to do so.
Novation Consulting director Elizabeth de Stadler says an argument can be made that Sanral should let affected people know their details have been compromised, although this will only become mandatory under POPI.
De Stadler explains the law is not in effect yet, because president Jacob Zuma has yet to set an effective date, and there is no indication of when that will happen. She adds companies will then have between one and three years to comply.
Under POPI, companies that suffer breaches will be told by the Information Regulator - an office yet to be set up - how to inform people of the risk, says De Stadler. She says this could be in person, or in the form of a newspaper advertisement, or a notice on a Web site, which carries with it reputational risk.
De Stadler adds Sanral most certainly has an ethical duty to inform those whose accounts have been accessed. She notes the flaw is a breach of the common law right to privacy.
Own goal
Local Web and digital media lawyer Paul Jacobson says people who have registered have a legitimate expectation of privacy, but the security flaw is a breach of Sanral's own privacy policy.
Sanral's e-toll privacy policy states "we will take all reasonable measures to protect your personal information and keep it confidential" and "ETC [the consortium running e-tolls] shall not disclose personal information received from you unless you consent thereto".

Jacobson says there is a big disconnect between the policy and what happened in practice. He adds people whose data has been compromised may wish to sue, but would battle to prove it was Sanral's negligence that led to that information being used to inflict damages.
The latest flaw is the strongest argument against registering to use Gauteng's electronic freeways, says Jacobson. He says registration exposes a lot of concentrated information, and usernames can easily be worked out, based on other information, such as e-mail addresses.
Although the fact of another security issue does not surprise Jacobson - due to the lack of proper implementation already evidenced - he is taken aback by the simplicity of the hole. "They've actually created a back door for themselves."
Additional reporting by Bonnie Tubbs.


