Kaspersky Lab is analysing an unusual malware attack, that it says is a curious mix of old-school programming and advanced sandbox-evading exploits.
Designed for cyber espionage purposes, the malware has targeted government officials in more than 20 countries.
Earlier this month, network security firm FireEye discovered an Adobe Reader zero-day exploit which is used to drop an advanced, and previously unknown, piece of malware.
Kaspersky Lab's team of experts, in conjunction with CrySys Lab, then analysed a series of security incidents involving the use of this exploit, and a new, customised malicious program the company dubbed MiniDuke.
"We called this new malware 'ItaDuke' because it reminded us of Duqu and because of the ancient Italian comments in the shellcode copied from Dante Aligheri's Divine Comedy," says the company.
According to the security firm, the MiniDuke backdoor has been used to attack multiple government entities and institutions worldwide during the past week. "Since the original announcement, we have observed several new attacks using the same exploit (CVE-2013-0640) which drop other malware. Between these, we've observed a couple of incidents which are so unusual in many ways that we decided to analyse them in depth."
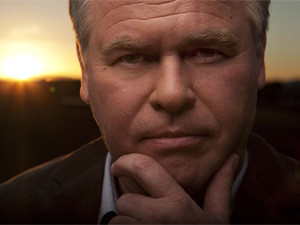
"This is a very unusual cyber attack," says Eugene Kaspersky, founder and CEO of Kaspersky Lab. "I remember this style of malicious programming from the end of the 1990s and the beginning of the 2000s. I wonder if these types of malware writers, who have been in hibernation for more than a decade, have suddenly awoken and joined the sophisticated group of threat actors active in the cyber world."
He says, in the past, these elite, "old school" malware writers were highly skilled at creating complex viruses, and are now combining these skills with the newly advanced sandbox-evading exploits to target government entities and research institutions in several countries.
Kaspersky has observed 59 unique victims in 23 countries: Belgium, Brazil, Bulgaria, Czech Republic, Georgia, Germany, Hungary, Ireland, Israel, Japan, Latvia, Lebanon, Lithuania, Montenegro, Portugal, Romania, Russian Federation, Slovenia, Spain, Turkey, Ukraine, UK and the US.
In addition, MiniDuke's creators are still active, and created malware as recently as 20 February.
How it works
Social engineering techniques have been used to compromise the victims. Malicious PDF files, that are well-crafted, were sent to the targets. The PDFs contained fabricated human rights seminar information and Ukraine's foreign policy and NATO membership plans.
However, the PDFs were rigged with exploits attacking Adobe Reader versions 9, 10 and 11, bypassing its sandbox, or isolated operating environment for unknown and untrusted applications.
Once the system has been breached, a small downloader, only 20KB in size, is dropped onto the victim's disc. This downloader is unique per system and contains a customised backdoor written in Assembler.
"When loaded at system boot, the downloader uses a set of mathematical calculations to determine the computer's unique fingerprint, and in turn uses this data to uniquely encrypt its communications later."
If the target system meets the pre-defined requirements, without the user's knowledge, the malware uses Twitter to start looking for specific tweets from pre-made accounts that were created by MiniDuke's command and control (C2) operators. The tweets maintain specific tags labelling encrypted URLs for the backdoors.
These URLs provide access to the C2s, which then provide potential commands and encrypted transfers of additional backdoors onto the system via GIF files.
Kaspersky says it would seem the MiniDuke's creators provide a dynamic backup system that can also remain undetected. If Twitter isn't working or the accounts are down, the malware can use Google Search to find the encrypted strings to the next C2.
Due to this model's flexibility, the operators are able to constantly change how their backdoors retrieve further commands or malcode as needed.
"Once the infected system locates the C2, it receives encrypted backdoors that are obfuscated within GIF files and disguised as pictures that appear on a victim's machine."
Once downloaded to the machine, they can fetch a larger backdoor, which then uses functions such as copy file, move file, remove file, make directory, kill process, and download and execute new malware and lateral movement tools.
"The final stage backdoor connects to two servers, one in Panama and one in Turkey, to receive the instructions from the attackers," says Kaspersky.
"Based on our experience, this is a unique and very strange attack. The many different targets hit in separate countries, together with the high profile appearance of the decoy documents and the weird backdoor functionality, indicate an unusual threat actor.
"Some of the elements remind us of both Duqu and Red October, such as the minimalistic approach, hacked servers, encrypted channels but also the typology of the victims," concludes Kaspersky.

